Hey guys!
In this article I would like to share with you a project that I have been developing since November 2018 and today has more than 4,500 lines of code, which is a very complete Security Checklist (probably the most complete and comprehensive you will find on the Internet), with more than 70 Security items to validate your database, including configurations and parameters, permissions, programming objects and much more!
After seeing so many companies, developers (and sometimes DBA's themselves) neglect the security aspect, where we see environments in which the application uses the user “sa”, we find thousands of connection attempts with incorrect passwords and no one does anything, environments WITHOUT BACKUP and many other absurdities, we decided to create a very practical and easy way to quickly get an overview of how the instance's security is, in a friendly format and with technical information at the same time, and which allows you to easily export to Excel and demonstrate the various problems to the client. found, the impact it can have on the environment and how to resolve it.
Discover the definitive solution to the vast majority of your SQL Server security problems in this article.
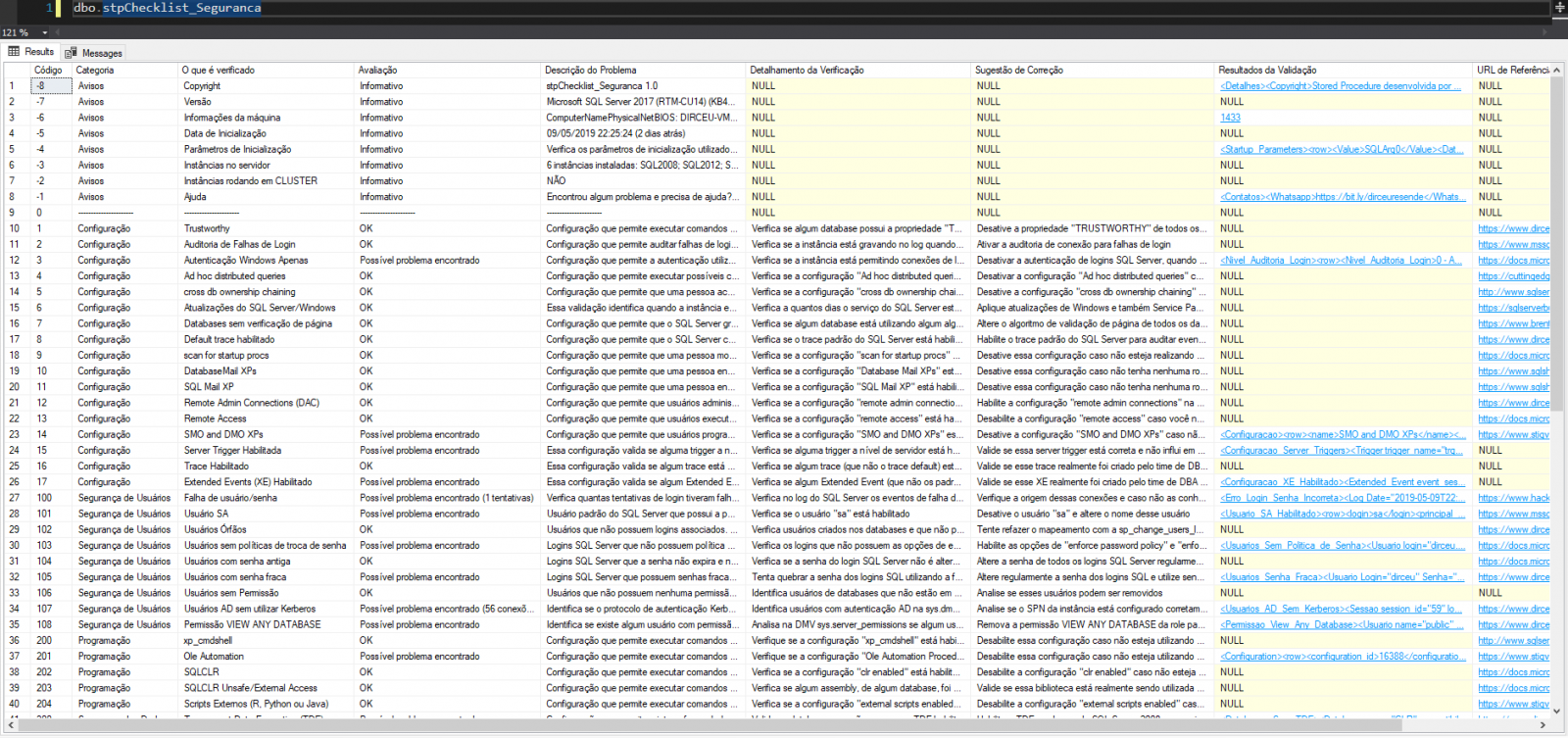
The scan results are organized as follows:
- Code: Just a unique number to make it easier to identify the verification item, including when I release the English version (spoiler!!)
- Category: A way to group the checks according to a logical category that I imagined for these validations
- What is checked: Check title, which is a summary of what this item is validating in the database
- Assessment: It is the result of validation. It informs if the item passed validation (OK), if it is just an informative item or if a POSSIBLE problem has been identified
- Problem Description: A brief explanation of why this item is being checked and what security risk it may pose to us
- Verification Details: More technical and specific details of what is being checked on the instance
- Correction Suggestion: Some guidance on how to correct or work around the possible problem identified by Stored Procedure
- Validation Results: XML that returns the records that caused the validation to fail and the identified artifacts (some items are limited to TOP(N) records, as there may be many records returned in the XML)
- Referral URL: Link to an article or documentation that can add or help in understanding this verification item
If the excuse for not dealing with security in your company was not having a practical and easy way to identify breaches, not knowing how to resolve them or not knowing what the security problems were, your excuses are over TODAY! This will never be a problem for you again.
This is a project that I use on several clients here at Fabrício Lima – BD Solutions, one of the best database and BI consultancies in Brazil, and is the result of a lot of study, testing and technical discussions with several great data professionals and after talking to Fabrício, we decided to release this in a FREE for the entire technical community.
After using sp_Blitz, from the legend Brent Ozar, for so long, I always found it incredible how practical and simple it was for identifying various performance, maintenance, auditing and some security items. Thinking about something just as practical, I was inspired by this idea to develop stpChecklist_Seguranca, trying to deliver something very “F5 version” to you.
This is not Dirceu's or Fabrício's project, but yours. For this reason, I am releasing the code for this Stored Procedure on Github, so that you can all download it, use it in your environments and help make it better and better through commits and pull requests to bring new features and fixes:
– https://github.com/dirceuresende/checklist_seguranca (source code)
Don't forget to follow my safety articles! This is an increasingly popular topic in Brazil, especially after the LGPD (General Data Protection Law), and for this reason, I launched the course Security in SQL Server – Module 1, where I will go through each of these security items and explain them in the smallest details, with exclusive examples and demonstrate how they can harm the instance and how we can deal with them.
No more searching through various websites and dozens of articles and best practice manuals where people tell you that “you should disable this”, but without convincingly explaining why and without technical arguments as to how this could harm your environment.
I hope you like this Procedure, a big hug to you and see you next time!



Comments (0)
Loading comments...